Sarnia drug investigation leads to arrest in Petrolia
Identity theft a concern after hospital hack
November 10, 2023
Heather Wright/The Independent
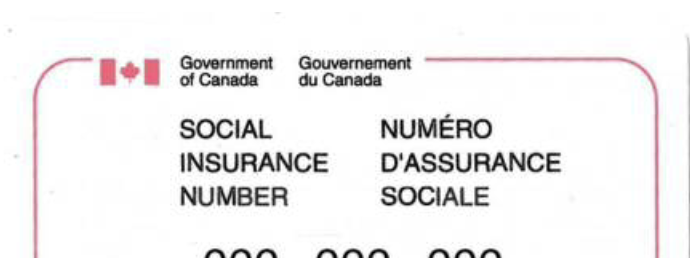
Bluewater Health says information from 269,000 patients – from 5.6 million visits – is in the hands of hackers. But what does that mean for the people whose names, medical conditions, and in some cases, social insurance numbers are now circulating the dark web?
The Independent contacted two experts in the field. Brett Callow – a threat analyst with the international security company Emsisoft and the head of DataBreaches.net – a blog dedicated to personal data security breaches.
Callow, who works for Emsisoft in Canada, says the hackers initially are looking for cash from the hospital. But when that fails, they start dumping any personal information they can find on the dark web.
In Bluewater Health’s case, the first information dump was Nov. 2 and the latest was Sunday. The only thing left to be dispersed now is the hospital’s data base.
Callow says once it is on the web, patients are vulnerable to identity fraud.
DataBreaches.net first identified the hackers at Bluewater Health as Daixin. For the past seven years, Dissent (a pseudonym) has been following cyber attacks in the medical field.
“If I have your name and identity information, can I open up an account in your name … I’ll get electrical services, I’ll get water services, I could get maybe health care services,” they tell The Independent. “Maybe I can start a corporation somewhere offshore in your name and open up a bank account, using that identity information, and then send all kinds of funds to that bank account.”
Dissent says people living in Canada illegally may troll the dark web to find identity information for sale to get a driver’s licence or government ID.
“It doesn’t sell for a lot on the dark web, because there’s just so much information out there, flooding the market by now.”
Dissent says hackers who didn’t receive cash from their primary victims – in this case the hospitals – may start extorting the patients, including using medical issues that could affect their employment, mental health problems even procedures like abortion.
“The data were sensitive and confidential info of named patients with their demographic info as well as health-related and account-related info. Many of the entries go back to service dates years ago, but they also included some current records. The records include dozens of fields including what service treated the patient (e.g., surgery, psychiatry) and when patients did not want any info given out about them to family or anyone. That ship has now sailed for them.
“There’s all kinds of sensitive things and health records that people want protected for a variety of reasons.
“If the victim entity doesn’t pay demands, they start picking up the phone, and contacting the patients directly and say, ‘Hey, I’m looking at your records here. If you don’t want this all over the internet, pay me $2,500.’…It’s gotten really ugly over the years.”
Callow says other businesses could also be threatened by the fallout.
“The type of thing we’ve seen in previous cases, the attackers have used the data to submit a fake invoice, for example, to a company’s supplier. That fake invoice actually carries banking information that’s under their control from accounts that are under their control. Potentially one crime, namely, the attack on the hospital, can lead to a multitude of others.”
Monday, the hospitals and Transform Services released more information about what data they believe is missing or exposed. All five hospitals affected by the Daixin attack say some employee records were accessed. And in those cases, employees were given access to two years of free credit monitoring to make sure their information isn’t being used by criminals.
What information has been shared directly with patients isn’t as clear.
The hospitals have been in contact with the Ontario’s Information and Privacy office as required by the Personal Health Information Privacy Act.
It also requires health care providers to take precautions to safeguard against theft, loss, as well as unauthorized collection, use, disclosure, copying, modification or disposal of your personal health information.
Health care organizations must “notify you, at the first reasonable opportunity, of the theft or loss or of the unauthorized use or disclosure of personal health information” and “of any uses and disclosures of your personal health information that occurred outside of their information practices and without your consent.”
Dissent of DataBreaches.net that notification is very important for patients, even though hospitals and their insurers often “keep the lid on everything” about the hack.
“They claim it’s best practices – but it is only best practices from their side of the equation.
“It’s not best practices, as far as I’m concerned, from the patient side of the equation, because I think the public needs to know if they’re at risk so they can take steps to protect themselves.”
Canada Revenue Agency warns people not to provide SIN numbers on job applications or rental agreements saying in the wrong hands, your SIN could lead to:
- an invasion of privacy
- identify theft
- loss of government benefits, tax refunds or bank credits
If someone uses your SIN to commit fraud, it could ruin your credit rating. Someone could also use your SIN to work illegally. In this case, the Canada Revenue Agency (CRA) may expect you to pay tax on income you did not receive.
It adds if you have been affected by a data breach, contact Canada’s 2 major credit bureaus to monitor your file.
- Equifax: 1-800-465-7166
- TransUnion: 1-800-663-9980
Regularly review your banking and credit card statements, especially after the credit monitoring service ends. Bluewater Health has committed to paying for credit monitoring for two years for the 20,000 people whose social insurance numbers have been stolen.
If you notice any suspicious activity, immediately report it to the police, contact the Canadian Anti-Fraud Centre, and inform Service Canada to reduce the potential impact.
Service Canada does not issue a new SIN for those affected by a data breach.

Sarnia drug investigation leads to arrest in Petrolia
June 30, 2025
Read More

Brooke-Alvinston gets up to $1M to repair arena floor
June 30, 2025
Read More

Brooke-Alvinston assault
June 27, 2025
Read More

Inn of the Good Shepherd looking for new leader as Vanni announces coming retirement
June 27, 2025
Read More
